

Cyber Security
Overview
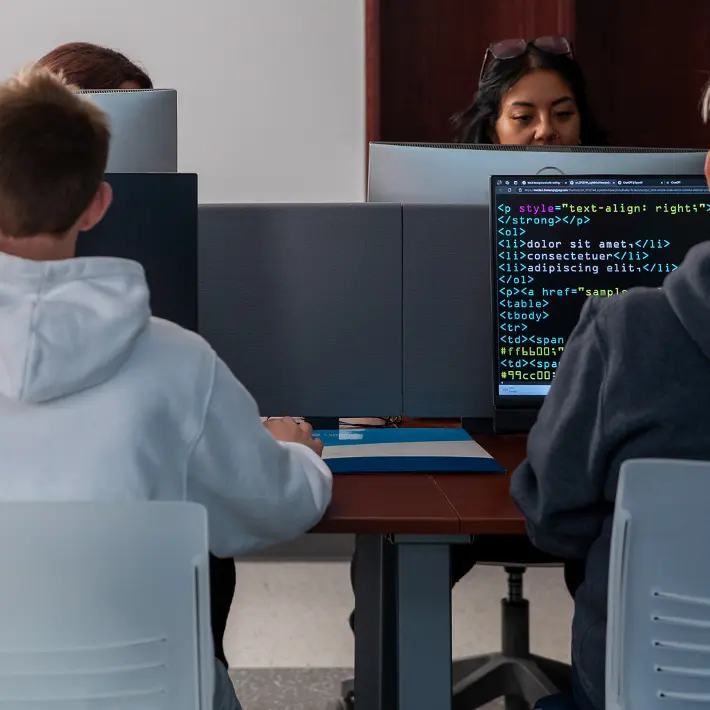
Develop highly marketable skills that are required in the burgeoning cyber security field.
The Cyber Security, Ontario College Graduate Certificate Program will provide students with key concepts of information security, technical and practical job skills necessary to secure, protect and defend network infrastructures and an organization’s valuable data assets.
The program curriculum provides students with a broad understanding of cyber security concepts, industry best practices for information security and key security concepts that will protect an organization against fraud, data breaches and other vulnerabilities. The Cyber Security program is designed to prepare information and cyber security professionals with the ability to manage, provide policies, standards, procedures, guidelines, policy framework, assess and mitigate risk and integrate advanced security solutions.
The growing internet security sector requires an in-depth understanding of cyber security issues, and fundamental internet architecture and protocols. In addition, network security skills such as packet, vulnerability, exploit analysis, and cyber security research are also discussed. Graduates will develop highly marketable skills that are required in the burgeoning cyber security field.
Admission Requirements
- Information Technology or computer related degree or diploma
- Equivalent work experience as determined by Lambton College
-or-
Costs
- Year 1 $4,769.99
Please Note: These fees apply to the 2025-2026 academic year and are subject to change. Fees do not include books (unless specifically noted), supplies or living costs.
OSAP Eligible
This program is OSAP eligible. OSAP is a needs-based Federal and Provincial student loan and grant program that is calculated based on your personal financial situation and the cost of your education expenses. If you are registered as a full-time student (minimum 60% course load), you may qualify for assistance. OSAP does not always provide assistance to cover all of your educational and living costs.
Technology Requirements
In order to keep pace with the requirements of each and every course in your program, Lambton College requires that each student have access to a laptop while studying at our college.
Courses
Principles of Information Security
Students are introduced to the fundamental concepts, techniques and principles of securing information in computing environments. Students will gain a solid understanding of the key principles, technologies, and security best practices that are crucial for protecting digital assets, protecting privacy of sensitive data, and appropriately managing security risks. Key elements of information security will be taught in depth, including threat and risk assessment, risk management, access control security, cryptography and encryption, network security, identity access management and incident response. Students will learn hands-on techniques that are critical to protect sensitive information from unauthorized exposure, modification, disclosure, and destruction.
Linux, Firewalls & VPN’s
This course explores network security basics, including how hackers access online networks and the use of Firewalls and VPNs to provide security countermeasures. Students focus on both managerial and technical aspects of security. Coverage includes packet filtering, authentication, proxy servers, encryption, bastion hosts, virtual private networks (VPNs), log file maintenance, and intrusion detection systems.
Computer Forensics & Investigation
This course introduces students to the principles and practices of digital forensics and investigation. Students will learn how to identify, acquire, preserve, and analyze digital evidence using industry tools and techniques. Topics include forensic methodology, evidence handling, file system and operating system analysis, event log collection, and forensic triage. Student will also explore the integration of forensic investigations into security operations, including SIEM log analysis and incident response procedures. Emphasis is placed on professional conduct, chain of custody, and the ability to communicate forensic findings clearly in written reports.
Mobile Application Security Design
This course provides students with concepts of discovering and exploiting flaws in mobile applications on the iOS and Android platforms. Students are introduced to a proven methodology for approaching mobile application assessments and the techniques used to prevent, disrupt and remediate the various types of attacks. Coverage includes data storage, cryptography, transport layers, data leakage, injection attacks, runtime manipulation, security controls, and cross-platform apps, with vulnerabilities highlighted and detailed information on the methods hackers use to get around standard security.
Operating Systems Security – Windows
Preparing students to recognize and understand the inherent vulnerabilities of Windows systems by using and understanding tools and techniques to decrease the risks arising from vulnerabilities in Microsoft Operating Systems and applications, this course introduces defence strategies through understanding of system and file permissions, password and account security, the Windows Registry, Malware prevention, encryption, and Directory Service management via policies.
Security Policies
Students will recognize the significance of security policies in safeguarding the organization's assets, mitigating risks, and adhering to regulatory requirements. Students will explore the fundamental concepts, principles, methodologies, and techniques associated with developing, implementing, and enforcing security policies across an organization.
Legal & Ethical Issues in IT Security
This course examines the evolving relationship between information technology, cybersecurity, and the legal, ethical, and regulatory frameworks that shape their use. Students will develop a strong understanding of the key legal obligations and ethical challenges facing security professionals, with emphasis on Canadian laws, global regulations, and professional codes of conduct. Topics include privacy rights, data protection, cybersecurity law, intellectual property, digital governance, and the societal impact of emerging technologies. Real-world case studies, legal frameworks, and ethical scenarios will be used to build students' ability to critically evaluate complex issues, assess risk, and navigate grey areas in decision-making. By the end of the course, students will be able to analyze, and articulate legal and ethical arguments related to cybersecurity incidents, and make informed, defensible decisions that consider diverse perspectives, regulatory requirements, and the broader consequences in today's interconnected digital landscape.
Ethical Hacking & Network Defense
This course prepares students to assess and then correct vulnerabilities present within information systems. Students are introduced to tools and penetration testing methodologies used by ethical hackers. What and who ethical hackers are and how they protect corporate and government data from cyber-attacks is discussed. Methods and tools used in attacks and their countermeasures as well as available security resources and attack "types" systems are also investigated.
Network Security & Penetration Testing
This course provides students with a comprehensive foundation in network security and penetration testing, combining theoretical principles with practical application. Learners will explore threats, vulnerabilities, and attacker methodologies including reconnaissance, scanning, exploitation, and post-exploitation. In a controlled lab environment, students gain hands-on experience with ethical penetration testing while upholding legal and professional responsibilities. Topics include, network architectures, secure protocols, encryption, defensive technologies (firewalls, IDS/IPS, VPNs) malware, phishing, DoS/DDoS, and ransomware. Students also examine cloud, web, Linux/Windows, and container vulnerabilities. Labs use industry-standard tools (Nmap, Wireshark, Metasploit, Burp Suite). Emphasis is placed on documentation and reporting, requiring students to present findings in professional security reports. By course end, students will be able to identify vulnerabilities, implement defenses, and contribute effectively to incident handling and recovery.
Hacker Techniques, Tools & Incident Handling
This course provides students with a detailed exposure to the methods, tools, and strategies used by bad actors (i.e. hackers) to breach and compromise computer systems and networks. Students will explore various hacking techniques and acquire hands-on experience in incident handling and response. Students will get into the mindset of hackers, gaining insights into their motives, methodologies, and techniques. They will learn about common attack vectors including network scanning, vulnerability exploitation, password cracking, social engineering, and malware deployment. By gaining exposure to the techniques employed by hackers, students will be equipped to defend and secure computer systems and networks against potential risks and threats. The course covers a wide variety of tools and technologies used in both offensive and defensive security. Students will have opportunities to explore popular hacking tools, including network analyzers, vulnerability scanners, password-cracking utilities, and intrusion detection systems. Practical exercises and simulations will enable students to apply these tools in real-world scenarios, honing their skills in identifying, mitigating, and responding to security incidents. The incident handling aspect of the course focuses on preparing students to effectively respond to security incidents. Students will develop incident response plans, and practice analyzing and containing security breaches within the boundaries of the law and respecting individual privacy rights.
Wireless & Mobile Device Security
Students will acquire an understanding of the principles, techniques, and best practices for securing wireless networks and mobile devices. The swift evolution of wireless communication technologies and the prevalent use of mobile devices have given birth to new security challenges that need to be addressed to protect sensitive information from unauthorized exposure and modification and ensure availability of wireless networks. Students will explore several wireless technologies, including Wi-Fi, Bluetooth, and cellular networks, and learn about the vulnerabilities and threats geared towards these technologies. Students will also learn about security protocols and mechanisms that are used to secure wireless networks and mobile devices, including authentication, encryption, access control, and intrusion detection systems.
Capstone Information Security Project
This course integrates the knowledge and skills students have obtained throughout the program. Emphasis is placed on security policy, process planning, procedure definition, business continuity, and systems security architecture. Upon completion, students are able to design and implement comprehensive information security architecture from the planning and design phase through presentation of the final product.
Contact
Continuing Education
Room B2-280
Program Information
After Graduation
Employment Opportunities
Career positions may include, but are not limited to:
- IT Consultant
- Computer Systems Analyst
- Information Security Analyst
- Information Security Quality Assurance Analyst
- Systems Security Analyst
More Information
Prepare for Success
Variations due to Section
Remember to review the important dates associated with this program - some deadlines may be different depending on how your program is delivered and what section you're enrolled in.
Technology Requirements
It is recommended that you use a Windows laptop for your coursework. While other devices like MacBooks or Chromebooks might work for some tasks, they may not support all the software required for your program. If you're unsure, check with your professors before buying.
Internet Speed Requirements
To get the best experience while learning online, we recommend having an internet connection with at least 40 Mbps download speed and 10 Mbps upload speed. This will help you use video calls, attend online lectures, and access other learning tools smoothly.
Because students live in many different areas, we can't suggest a specific internet provider. You'll need to check with local companies to find one that works best for you.
Laptop Requirements
In order to access the internet and virtually-delivered software and courseware, student laptops should include the following at a minimum. By meeting the following specifications, students will be equipped to access software and courseware on their laptop through the internet:
- Intel i5 8th Gen Processor or equivalent
- 8GB of RAM
- 100 GB HDD or more
- Webcam with a microphone
- Wi-Fi capable (802.11n/ac 5GHz)
- Windows 11 operating system
Mobile Device
Students will require a mobile device (smartphone) for:
- Accessing your digital student ID
- Using campus applications and services
Software
To ensure students are getting the most our of their classroom experience, some software will be required.
Lambton College has made this software easily accessible online. Students can leverage our Microsoft Office 365 software packages and services. In addition, much of the software you require for your courses will be available on demand for use on any device - on or off campus.